Enterprise-grade security built for trusted guidance
Financial advisors across the country use Pontera to deliver secure 401(k) guidance to retirement savers.
SOC 2 Type 2
ISO/IEC 27001:2022
California Consumer Privacy Act
Our promise
Security and privacy are core to how we build and operate Pontera. We apply layered security approach across our infrastructure and SaaS platform, aligned with leading frameworks such as NIST CSF and ISO/IEC 27001. Our practices are continuously reviewed and evolved to reflect evolving threats and industry best practices.

ISO/IEC 27001:2022
Pontera is certified under ISO/IEC 27001:2022, with ISO/IEC 27017 and ISO/IEC 27018 as part of our audited scope. Together, these internationally recognized standards affirm our security, cloud controls, and data-privacy protections.

ISO/IEC 27018
Pontera is certified for ISO/IEC 27018, the international standard for privacy in cloud computing. It ensures we implement strong controls to protect personally identifiable information (PII) stored and processed in the cloud.

ISO/IEC 27017
Pontera is certified for ISO/IEC 27017, which provides additional security controls specifically for cloud services. This demonstrates our commitment to protecting customer data in cloud environments through industry-recognized best practices.

SOC 2 Type 2
SOC 2 Type 2 certification demonstrates our compliance with industry-leading standards for information security, including implementation of stringent security and privacy practices. Available upon request, Pontera's SOC 2 Type 2 certification is issued through Ernst & Young.
California Consumer Privacy Act
Pontera complies with privacy regulations, including the California Consumer Privacy Act to ensure the lawful and ethical handling of personal data.

Secure by design
As part of our commitment to building safer products, Pontera has joined the CISA Secure by Design pledge. This reflects our intent to keep improving and to make secure-by-default choices that protect our customers and their data.
Access control
Pontera follows a modern, risk-based access control framework designed to ensure that users receive only the access they need—and only when they need it. Strong authentication, contextual checks, and temporary, approval-based access for sensitive operations help maintain a secure environment while supporting operational efficiency.
Workforce practices
At Pontera, our team is committed to developing and enacting data privacy and information security practices that align with industry benchmarks and best practices. All employees undergo background checks, sign non-disclosure agreements, and complete mandatory security and privacy training programs to create a secure environment.
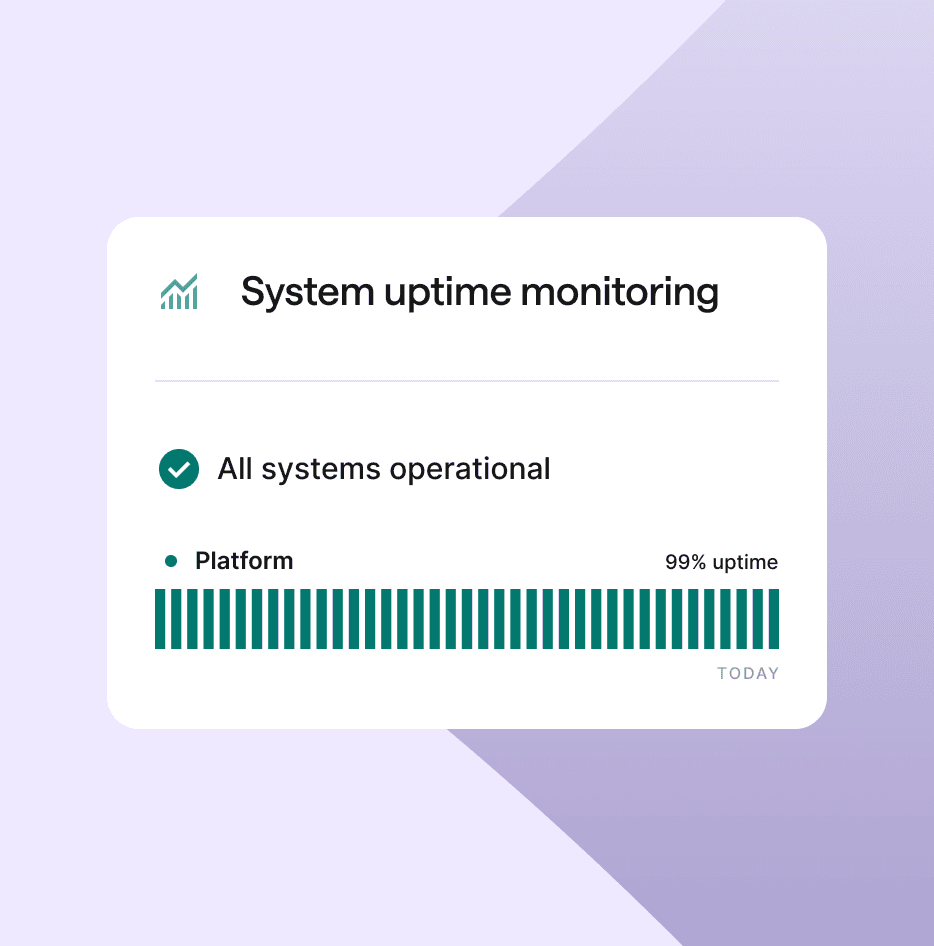
Reliability
Built with reliability in mind
Availability and continuity
Pontera deploys system uptime monitoring and 24/7 priority support. Our system is designed for resiliency and to withstand potential disruptions. Disaster Recovery Plans (DRP) and Business Continuity Plans (BCP) are continuously tested and updated to mitigate risks and allow the quick restoration of services in the event of unforeseen circumstances.
Backup and recovery
Secure and routine backups ensure the availability of customer data and enable speedy recovery in the event of data loss or system failure.